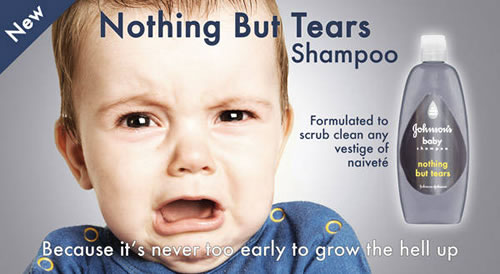
My friend Chris sent me this today, and I liked it so much I had to post it here...

This is something that I find fascinating, and it is more common than one would expect. I am not sure why people don't secure their wireless, whether they don't care or just can't because the instructions on how to do so are difficult to understand. And it can be, as there are numerous options. In my neighborhood, I can see several access points. Thankfully, most are secure, but a few are not. If a wireless network is unsecure, that can leave any computer on that network vulnerable. Now-a-days, even if you use WEP encryption, you are not fully secure. There are several ways to get the encryption keys, easy enough even for the most inept script kiddie. Another danger with unsecure networks, and this is a biggie, is that naughty people may do bad things over the connection like kiddie porn and threatening emails. If the traffic gets traced, it comes back to the owner of access point. Not good.
My wireless network is probably the strongest in the neighborhood. I use a Cisco 1231 b/g wireless access point (all of my network equipment...router, switch, access point...is real Cisco stuff. I am a CCNA after all!) I have two antennas, a high-gain yagi directional antenna on the roof pointed to my parent's house, and a smaller omnidirectional in the ceiling of the hallway. I'm pretty sure every wardriver in the Greater Dayton area has been to my neighborhood to get on my juicy 6 Mb DSL.
I use WPA for connection authentication, and TKIP for data encryption from the computer to the access point. You have to know the pre-shared WPA key to get access, then the TKIP encrypts the data so a sniffer would see gobbledygook rather than your data. At least it is pretty well protected, for now, since encryption methods are being cracked all the time. For even better security, you can apply MAC address filtering, thus only allowing connections from any physical network card which you have registered with your access point. I have not done this because I have lots of wireless devices and work on computers at home, and it would be a chore to track all of that.
I plan on implementing a RADIUS server on my network so I can dump the "pre-shared key" on WPA, and implement 802.1x. This will allow me to set up logins on a server, and the computer or device will have to authenticate by an appropriate username and password. This is also known as WPA-Enterprise and is usually used in large companies. I was working on this before I came down with cancer and have not gotten back to it.
I am implementing a wireless solution at work using a centralized Cisco controller, with all the fancy-schmancy security features. This is a great solution, albeit expensive. I have had great success with it so far, and I am excited to get more access points installed. I have also learned a great deal about wireless and its associated security functions, and I am really eager to learn more.
So, if your wireless is open and exposed to God and everybody, GET IT SECURE!

This is something that I find fascinating, and it is more common than one would expect. I am not sure why people don't secure their wireless, whether they don't care or just can't because the instructions on how to do so are difficult to understand. And it can be, as there are numerous options. In my neighborhood, I can see several access points. Thankfully, most are secure, but a few are not. If a wireless network is unsecure, that can leave any computer on that network vulnerable. Now-a-days, even if you use WEP encryption, you are not fully secure. There are several ways to get the encryption keys, easy enough even for the most inept script kiddie. Another danger with unsecure networks, and this is a biggie, is that naughty people may do bad things over the connection like kiddie porn and threatening emails. If the traffic gets traced, it comes back to the owner of access point. Not good.
My wireless network is probably the strongest in the neighborhood. I use a Cisco 1231 b/g wireless access point (all of my network equipment...router, switch, access point...is real Cisco stuff. I am a CCNA after all!) I have two antennas, a high-gain yagi directional antenna on the roof pointed to my parent's house, and a smaller omnidirectional in the ceiling of the hallway. I'm pretty sure every wardriver in the Greater Dayton area has been to my neighborhood to get on my juicy 6 Mb DSL.
I use WPA for connection authentication, and TKIP for data encryption from the computer to the access point. You have to know the pre-shared WPA key to get access, then the TKIP encrypts the data so a sniffer would see gobbledygook rather than your data. At least it is pretty well protected, for now, since encryption methods are being cracked all the time. For even better security, you can apply MAC address filtering, thus only allowing connections from any physical network card which you have registered with your access point. I have not done this because I have lots of wireless devices and work on computers at home, and it would be a chore to track all of that.
I plan on implementing a RADIUS server on my network so I can dump the "pre-shared key" on WPA, and implement 802.1x. This will allow me to set up logins on a server, and the computer or device will have to authenticate by an appropriate username and password. This is also known as WPA-Enterprise and is usually used in large companies. I was working on this before I came down with cancer and have not gotten back to it.
I am implementing a wireless solution at work using a centralized Cisco controller, with all the fancy-schmancy security features. This is a great solution, albeit expensive. I have had great success with it so far, and I am excited to get more access points installed. I have also learned a great deal about wireless and its associated security functions, and I am really eager to learn more.
So, if your wireless is open and exposed to God and everybody, GET IT SECURE!